Page 99 - ELT_1_1st April 2020_Vol 372_Part
P. 99
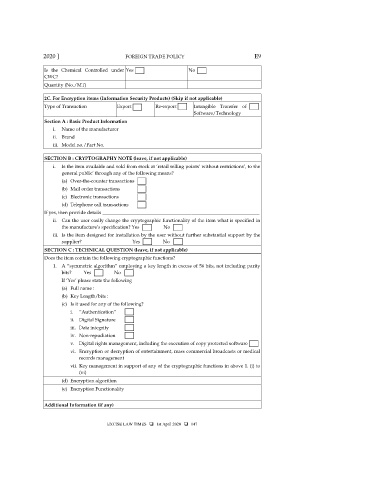
2020 ] FOREIGN TRADE POLICY E9
Is the Chemical Controlled under Yes No
CWC?
Quantity (No./MT)
2C. For Encryption items (Information Security Products) (Skip if not applicable)
Type of Transaction Export Re-export Intangible Transfer of
Software/Technology
Section A : Basic Product Information
i. Name of the manufacturer
ii. Brand
iii. Model no./Part No.
SECTION B : CRYPTOGRAPHY NOTE (leave, if not applicable)
i. Is the item available and sold from stock at ‘retail selling points’ without restrictions’, to the
general public’ through any of the following means?
(a) Over-the-counter transactions
(b) Mail order transactions
(c) Electronic transactions
(d) Telephone call transactions
If yes, then provide details _________________________________________________________________
ii. Can the user easily change the cryptographic functionality of the item what is specified in
the manufacture’s specification? Yes No
iii. Is the item designed for installation by the user without further substantial support by the
supplier? Yes No
SECTION C : TECHNICAL QUESTION (leave, if not applicable)
Does the item contain the following cryptographic functions?
1. A “symmetric algorithm” employing a key length in excess of 56 bits, not including parity
bits? Yes No
If ‘Yes’ please state the following
(a) Full name :
(b) Key Length/bits :
(c) Is it used for any of the following?
i. “Authentication”
ii. Digital Signature
iii. Data integrity
iv. Non-repudiation
v. Digital rights management, including the execution of copy protected software
vi. Encryption or decryption of entertainment, mass commercial broadcasts or medical
records management
vii. Key management in support of any of the cryptographic functions in above 1. (i) to
(vi)
(d) Encryption algorithm
(e) Encryption Functionality
Additional Information (if any)
EXCISE LAW TIMES 1st April 2020 147